Lưu ý chung
Lưu ý 1: Ở phần này, mình gặp rất nhiều trở ngại khi cố gắng xác định encoding type để chọn đúng công cụ bẻ khóa dãy encoding. Ví dụ như dựa vào các dấu gạch dưới ‘_’ giữa các cụm lớn ví dụ ‘Kxydrob_mokcob_mszrob’, mình có thể đoán nó là những từ có nghĩa nhưng ký tự đã bị đảo đi để biến nó thành vô nghĩa; dựa vào các dấu bằng ‘=’ ở cuối dãy để biết nó được encoding theo họ Base, có thể là Base64, Base32 vâng vâng; hoặc dựa vào các ký tự như .— -.. rất giống cách hoạt động của mã Morse, thế nhưng vẫn có rất nhiều dãy encoding mình gần như không xác định được dạng để crack.
Thế nên bạn nào biết cách xác định dạng encoding hoặc biết có công cụ nào có thể xác định hoàn hảo các dãy encoding bên dưới, thì xin comment hoặc chia sẻ lại bên dưới cho mọi người biết nhé.
Bạn nào muốn tìm hiểu thêm về cryptography có thể bấm vào tài liệu tại link này nhé:
https://www.tutorialspoint.com/cryptography/index.htm
Lưu ý 2: Cấu trúc lệnh netcat
nc <Machine IP> <port>
Lưu ý 3: Vì mỗi lần khởi động lại máy một địa chỉ IP mới sẽ được gán cho máy chủ CTF, nên IP của bạn không nhất thiết phải giống như trong bài nhé.
Lưu ý 4: Một điều khá dở của máy chủ CTF 100 Tryhackme đó là nó không lưu lại phần làm bài của bạn. Nghĩa là giả dụ như bạn đã làm được 10/19 câu của stage 1, bạn muốn để dành phần còn lại vào ngày hôm sau, thì qua ngày hôm sau, bạn phải làm lại những flags port knocking, là những flags mà khi bạn vượt qua, sẽ có những ports mới được mở ra cho bạn, ví dụ flag 7, thì bạn mới có thể làm tiếp được.
Lưu ý 5: Tryhackme chỉ cho thời hạn mặc định một máy hoạt động là 1 tiếng. Khi deploy máy, bạn có thêm click ‘Add 1 hour’ để có được 2 tiếng và bạn không thể click ‘Add 1 hour’ cho đến khi thời gian của bạn còn lại dưới 60 phút. Nếu bạn không gia hạn thời gian, máy sẽ tự động tắt khi hết thời gian dù cho bạn có đang làm việc với máy đi chăng nữa. Nên các bạn lưu ý nhớ theo dõi thời gian còn lại của máy nhé.
Lưu ý 6: ^C = ctrl + C
Link truy cập CTF 100:
tryhackme.com/jr/ctf100w1
The theme of stage 1 is about ciphering, text encoding and esolang. Nothing special here just wanted to test your skill.
Task 1-1: Flag 1 – The beginning of the end
Start your Nmap scanner and locate the open port.
$ nmap -Pn -p3000-3999 -v -T5 --min-parallelism 100 <Machine IP>
$ nmap -Pn 172.16.222.132
Starting Nmap 7.80 ( https://nmap.org ) at 2020-05-22 21:42 CEST
Nmap scan report for 172.16.222.132
Host is up (0.0014s latency).
Not shown: 998 filtered ports
PORT STATE SERVICE
3333/tcp open dec-notes
9999/tcp open abyss
Nmap done: 1 IP address (1 host up) scanned in 13.86 seconds
Nmap done: 1 IP address (1 host up) scanned in 13.86 seconds
$ nc 172.16.222.132 3333
***************************
* 100 Flags challenge *
***************************
Welcome to the THM point grabbing challenge!
The task is simple, find the flag and get the point
It can be hard or easy, IDK
To start the challenge, I need your address. So that I can send it to you.
> 172.16.222.1
Well done! Please take your first flag
flag 1: you_got_a_message
5 open ports is now opened for you! Hint: 4 digits and start with 3
Good luck!
^C
The terminal asking for your address. Enter the address according to your Tryhackme IP. Alright! We just capture our first flag. The terminal also mentions that there are 5 ports are being opened in the machine. Time to perform another Nmap scan.
Answer: you_got_a_message
Task 1-2: Flag 2 – ROT 13
Do another Nmap scan with the following command.
$ nmap -Pn -p3000-3999 -v -T5 --min-parallelism <Machine IP>
PORT STATE SERVICE
3333/tcp open dec-notes
3343/tcp open ms-cluster-net
3353/tcp open fatpipe
3363/tcp open nati-vi-server
3373/tcp open lavenir-lm
3383/tcp open esp-lm
$ nc 172.16.222.132 3343
Flag 2 challenge
Crack the following code
Guvf_vf_prnfre_pvcure
=> This_is_ceaser_cipher
Good job!
flag 2: qt8pm59jh5r49uqdwfw2
Just some numbering: 8989
We are now able to identify all the ports current open in the machine. Let kick start with port 3343.Upon accessing the port, you will be greeted with a message and an input field. The code can be deciphered using Rot 13 decode.Enter the plaintext and capture the flag. Take note of the number as we going to need it afterward.
Answer: qt8pm59jh5r49uqdwfw2
Task 1-3: Flag 3 – Ceaser cipher
Let’s move on to the next port (3353).This is a Ceaser cipher. keep click the plus sign (+) until you get a proper English word.
$ nc 172.16.222.132 3353
Flag 3 challenge
Crack the following code
Kxydrob_mokcob_mszrob
=>Another_ceaser_cipher
Good job!
flag 3: 5wdtc7jzk33qjauh5gxm
Just some numbering: 7431
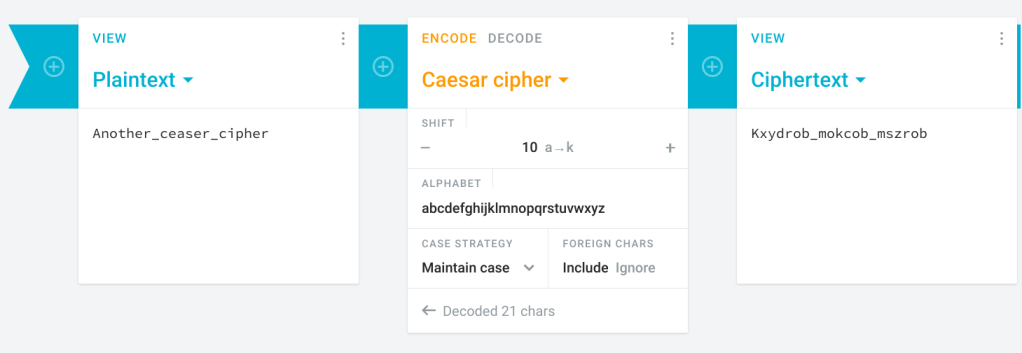
Answer: 5wdtc7jzk33qjauh5gxm
Task 1-4: Flag 4: Vigenere cipher
This task is a bit tricky. Let see what is inside the port 3363.Where is the key. Get it? Basically the key is where.
$ nc 172.16.222.132 3363
Flag 4 challenge
Crack the following code
where is the key
Ez_me_jnvrk_sb_fslv_afij
=> Is_in_front_of_your_eyes
Flag 4: sm8jvu8jxu7dz6s7qmsp
Just some numbering: 5667
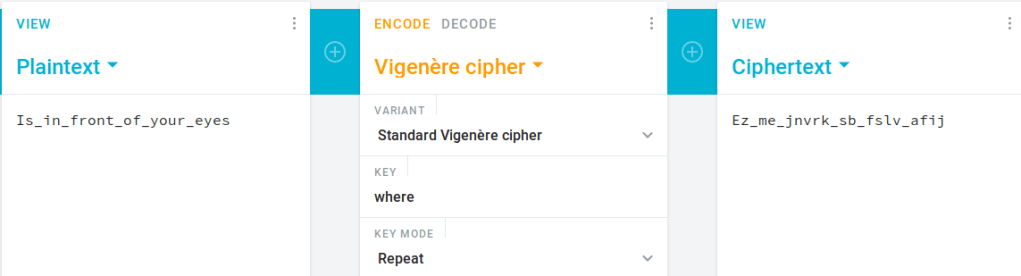
Answer: sm8jvu8jxu7dz6s7qmsp
Task 1-5: Flag 5 – Morse code
Next port (3373) please.Use a Morse code translator to yield the following results.
$ nc 172.16.222.132 3373
Flag 5 challenge
Crack the following code
-- --- .-. … . / -.-. --- -.. . / -… . . .--. / -… --- --- .--.
=> MORSE CODE BEEP BOOP
Good job!
flag 5: 2p3363hrava9fbq296ca
Just some numbering: 9332
Answer: 2p3363hrava9fbq296ca
Task 1-6: Flag 6 – Hex
Let’s hop on into next port (3383)This one easy, just translate the hex code into ASCII.
$ nc 172.16.222.132 3383
Flag 6 challenge
Crack the following code
59 6f 75 20 67 65 74 20 68 65 78 2d 65 64
=> You get hex-ed
Good job!
flag 6: skuj9359mqdm6sv8d8z6
Just some numbering: 3331
Answer: skuj9359mqdm6sv8d8z6
Task 1-7: Flag 7 – Silent
Did you get all 5 numbers from the previous task? The number is 8989 7431 5667 9332 3331. According to the order of the flags. Open up port 9999 and enter those numbers. (There is a reason I choose port 9999 as port knocking channel, use Nmap and check the name of the port)
$ nc 172.16.222.132 9999
**************************
Port knocking input
**************************
Hi user, please enter the port sequence
The format is (can be more than 4): PORT PORT PORT PORT
=> 8989 7431 5667 9332 3331
Something happen
Good luck!
Does something happen? Time to do another scan
$ nmap -Pn -p4000-4999 -v -T5 --min-parallelism 100 <Machine IP>
PORT STATE SERVICE
4000/tcp open remoteanything
Another open port. Let’s check it out
$ nc 172.16.222.132 4000
Congratulation! You have captured all the flag
Please go home, nothing to see here
Type 'exit' and leave this place
exit
^C
DO NOT TRUST ANYTHING IT SAID.
Keep silent by pressing enter and eventually it will open another path for you.If you get trolled, I’m truly sorry. The PORT PORT … mean there is another 5 port opened in the machine.
$ nc 172.16.222.132 4000
Congratulation! You have captured all the flag
Please go home, nothing to see here
Type 'exit' and leave this place
WHY are you here? Leave
Seriously? Nothing to see here!
GET LOST!
Please I beg you, LEAVE!
Oh my fking god, take it, JUST TAKE IT
flag 7: zmht7gg3q3ft7cmc942n
Please leave, thank you
PORT PORT PORT PORT PORT
8989 7431 5667 9332 3331
Ncat: Broken pipe.
Answer: zmht7gg3q3ft7cmc942n
Task 1-8: Flag 8 – Base64
Perform another Nmap scan.
$ nmap -Pn -p4000-4999 -v -T5 --min-parallelism 100 <Machine IP>
$ nc 172.16.222.132 4001
Flag 8 challenge
Crack the following code
QSBjb21tb24gYmFzZQ==
=> A common base
Good job!
flag 8: dmm32qvfkfwm6yjnw46k
Same old stuff: 10113
more challenges are ready to be solved. Let’s move on to port 4001.This is a base64 encoded text. Let’s decode the text.Take note of the number as you gonna need it later on.
Answer: dmm32qvfkfwm6yjnw46k
Task 1-9: Flag 9 – Base32
Let’s move on to the port 4002.This is base32.
$ nc 172.16.222.132 4002
Flag 9 challenge
Crack the following code
KRUGS4ZANFZSAYJAONWWC3DMMVZCAYTBONSQ====
=> This is a smaller base
Good job!
flag 9: fuf8mx74nph26f69mr97
Same old stuff: 10415
Answer: fuf8mx74nph26f69mr97
Task 1-10: Flag 10 – Base58
What inside port 4003?This is a base58. For your information, base58 is almost look-alike to base64 but it is not very well-known.
$ nc 172.16.222.132 4003
Flag 10 challenge
Crack the following code
4UFrmghikrDhdg9avkV9avpg4uHQmhvUf7GgRoCo
=> Look like a brother to base64
Good job!
flag 10: hud9bm8yc37md5b7t7mn
Same old stuff: 21033
Answer: hud9bm8yc37md5b7t7mn
Task 1-11: Flag 11 – Base85/ASCII85
Port 4004, onward!Base85 something looks like gibberish to us. Base85 or ASCII 85 contains all the readable ASCII code from decimal 33 to 117. Use the following decoder to decode the text.
$ nc 172.16.222.132 4004
Flag 11 challenge
Crack the following code
9lG&`+@/pn8P(%7BOPpi@ru:&
=> More ASCII character
Good job!
flag 11: 4xm43r2wajrsrbm4775d
Same old stuff: 35555
Answer: 4xm43r2wajrsrbm4775d
Task 1-12: Flag 12 – Base91
What does the port 4005 say?Hey, another gibberish. This is base91 encoded text and nobody gonna uses it.
$ nc 172.16.222.132 4005
Flag 12 challenge
Crack the following code
Erzg,W]@7RqSkb9jPD<:vz3B
=> More and More ASCII
Good job!
flag 12: qtfvbd7gbvyg9gww5jwj
Same old stuff: 25637
Answer: qtfvbd7gbvyg9gww5jwj
Task 1-13: Flag 13 – Recollection
Similarly to the task 1-7, collect all 5 numbers and reveal another path. The number can be ordered as (according to flag number) 10113 10415 21033 35555 25637. This order is not true, you need to reverse the order and become.25637 35555 21033 10415 10113.
$ nc 172.16.222.132 9999
********************
Port knocking input *
********************
Hi user, please enter the port sequence
The format is (can be more than 4): PORT PORT PORT PORT
=> 10113 10415 21033 35555 25637
Wrong sequence
Bye!
^C
$ nc 172.16.222.132 9999
********************
Port knocking input *
********************
Hi user, please enter the port sequence
The format is (can be more than 4): PORT PORT PORT PORT
=> 25637 35555 21033 10415 10113
Something happen
Good luck!
Use the number on port 9999 to open a new path.Perform another Nmap scan to find the path.
$ nmap -Pn -p6000-6999 -v -T5 --min-parallelism 100 <Machine IP>
PORT STATE SERVICE
6000/tcp open X11
Huh, port 6000. More challenges ahead!
$ nc 172.16.222.132 6000
Congratulation on getting this far
You are a worthy challenger
5 more gates are opened for you
Take this as your reward
flag 13: aehg24vwn5yyc8jz4tv5
Answer: aehg24vwn5yyc8jz4tv5
Task 1-14: Flag 14 – pikalang
Do another Nmap scan and I promise this is the last Nmap scan, haha.Alright, we located all 5 open ports. Let’s move on to the port 6010.What? We can’t understand this language.
PORT STATE SERVICE
6000/tcp closed X11
6010/tcp open x11
6020/tcp open x11
6030/tcp open x11
6040/tcp open x11
6050/tcp open arcserve
$ nc 172.16.222.132 6010
Flag 14 challenge
Crack the following code
pi pi pi pi pi pi pi pi pi pi pika pipi pi pipi pi pi pi pipi pi pi pi pi pi pi pi pipi pi pi pi pi pi pi pi pi pi pi pichu pichu pichu pichu ka chu pipi pipi pipi pi pi pi pi pi pi pi pi pi pi pikachu pipi pi pi pi pi pi pikachu pi pi pikachu ka ka ka ka ka ka ka ka ka ka pikachu pi pi pikachu pi pi pi pi pi pikachu pi pi pi pi pi pi pi pi pi pi pi pi pi pikachu pichu pichu pi pi pikachu pipi pipi ka ka ka ka ka ka ka ka ka ka ka ka pikachu pi pi pi pi pi pi pi pi pi pi pikachu pichu pichu pikachu pipi pi pi pi pi pi pi pi pi pi pi pi pi pi pi pi pi pi pikachu pichu pikachu pipi pipi pi pikachu pi pi pi pi pi pikachu ka ka ka ka ka ka ka ka ka pikachu pichu pi pi pi pi pikachu pichu pikachu pipi pipi ka pikachu pichu pi pikachu pichu pikachu pipi ka pikachu pipi ka ka ka pikachu pichu pikachu ka ka pikachu pipi pi pi pi pi pi pi pi pi pikachu ka ka pikachu pichu pi pi pi pi pi pi pikachu ka ka ka ka ka ka pikachu pichu pikachu pipi pipi ka ka pikachu ka pikachu ka ka ka ka pikachu pichu pi pi pikachu pipi pi pi pikachu pi pi pikachu ka pikachu
=> Pikachu is a type of electric pokemon
Good job!
flag 14: k2phhw85emq3v4njj5g6
You know the drill: 31031
Who let the Pikachu out? Actually this is an esolang called pikalang. Check this translator out.
Answer: k2phhw85emq3v4njj5g6
Task 1-15: Flag15 – Binaryfuck
Another esolang on port 6020.This is not an ordinary binary number, this is another esolang called binaryfuck. Check this translator.
$ nc 172.16.222.132 6020
Flag 15 challenge
Crack the following code
000000000000000000000000000000110010000010000000000010000000000000000000000010000000000000000000000000000000011011011011001111010010010000000000000000000000000000000000000000000100010000000000000100000100000000000000000000000000000000100011011000000100010010001001001001001001001001001001100000000000000000000000000000000100011011100010010001001001001001100000100000000000000000100011011100010000000000000000000000000000000000000000100011100010000100000000000000000000000100000000000000000100001001001001001001001001001001001001001100010001001100000000000000000000000100
=> This is not a binary
Good job!
flag 15: qtfvbd7gbvyg9gww5jwj
You know the drill: 50010
Answer: qtfvbd7gbvyg9gww5jwj
Task 1-16: Flag 16 – Spoon
Find the spoon on port 6030.This is another esolang named spoon. Try this translator.
$ nc 172.16.222.132 6030
Flag 16 challenge
Crack the following code
111111111100100010101011101011111110101111111111011011011011000001101001001000101001011111111111001010111001010000000000000000000000001010011011110010100100100000000000000000000000000000000010101111111111111001010000000000000000000000000000000001010011011001010010010111111111111111001010000000000001010000001010001010000001010
=> Fork and spoon
Good job!
flag 16: ckjug6sj88xuajfku72h
You know the drill: 7968
Answer: ckjug6sj88xuajfku72h
Task 1-17: Flag 17 – Reversefuck
Drop the bass on port 6040.Brainfuck is too mainstream, that is why I go for reversefuck. Use this translator.
$ nc 172.16.222.132 6040
Flag 17 challenge
Crack the following code
----------]<-<---<-------<---------->>>>+[<<<------------,<-,-----------------,+++++++++++++++++,-------------,-,++++++++++++++,>>--,<<----------,+++++++++,>>,<<++++,----------------,>---------------,--------,<++++,>+++,<-------,>+++,--------,
=> Reverse of brainfuck
Good job!
flag 17: x4xhrqx3ywzyx2jmgc5j
You know the drill: 20010
Answer: x4xhrqx3ywzyx2jmgc5j
Task 1-18: Flag 18 – Alphuck
Another brainfuck variation on port 6050.This is a variation of brainfuck, called alphuck. Use this translator.
$ nc 172.16.222.132 6050
Flag 18 challenge
Crack the following code
eeeeeeeeeepaeaeeeaeeeeeeeaeeeeeeeeeeccccisaaaeeeejaeeeeeeeeeeeeeeeeejiijejcceejaaiiiiiiiijiiijeejiiiiiijccjaaeeeeeeeeeeeeeeejiiiiiiiiiiiijiiijccjaaiiijeeeeeeeeeeeeeeeejiiiiiiiiiiiiiiiiijeeeeeeeejeeeeejiiiiiiiijeeeeeeeeeeeeeeejiiiiiiiiiiiiiiiiiijeeeeeeeej
=> Just like the brainfuck
Good job!
flag 18: kr2t9qcgt4ht9h6j5ydp
You know the drill: 6100
Answer: kr2t9qcgt4ht9h6j5ydp
Task 1-19: Until the next challenge.
Did you notice the numbering on the last 5 tasks? That is the port knocking sequence for stage two. The order should be31031 50010 7968 20010 6100. Use these number to unlock the port on stage 2.
If you have doubts about the sequence, you can perform a check on port 9999.
Answer: 31031 50010 7968 20010 6100
Source:
https://www.embeddedhacker.com/2019/11/hacking-walkthrough-thm-ctf-100-stage-1/
https://www.aldeid.com/wiki/TryHackMe-CTF-100/stage1#.5BTask_1.5D_Stage_1

